By Sufian Al-Tal
Construction of the aircraft carrier USS Gerald R. Ford began in 2005. Its plans were fully prepared and built on defensive foundations that, based on the data and military science available up to 2005, made it unsinkable.
However, between 2005 and 2025, 20 years of scientific and military development passed, and new sciences emerged and clashed, which the aircraft carrier’s plans and designs at the time did not take into account. In addition, the aircraft carrier USS Enterprise, which entered service in 1961, was officially decommissioned on February 3, 2017, after more than 55 years.
Thinking strategically?
The aircraft carrier USS Gerald R. Ford is one of the most advanced warships in modern history and is often referred to as “unsinkable.” However, while this description is valid in its military context, it remains relative, not absolute. The real question is not whether sinking it is theoretically possible, but whether its defensive design philosophy can still keep pace with the rapid scientific and military advancements the world witnessed between 2005 and 2025.
Work on the design of the aircraft carrier began at the start of the new millennium. This means that the engineering plans and defensive doctrines upon which it was based were grounded in the military science, weapons technologies, and anticipated threat patterns available at the time.
At that time, traditional naval threats, such as anti-ship and anti-submarine missiles, were known and incorporated into existing defense systems. This allowed the USS Gerald R. Ford aircraft carrier to be designed as a highly fortified, multi-system vessel capable of absorbing damage without losing combat capability. From an engineering perspective, no naval vessel is designed with the absolute impossibility of sinking in mind, but rather with the principle of survivability after being hit.
The aircraft carrier USS Gerald R. Ford relies on a complex internal layout that minimizes the risk of cascading sinking, advanced fire suppression and damage control systems, and the ability to continue operating even after sustaining direct hits. However, all of this assumes a specific type of threat and relatively conventional combat scenarios within the parameters of that era.
Hypersonic missiles
Between 2005 and 2025, the military world witnessed significant developments that were not part of the initial design calculations. Among the most prominent of these are the emergence of hypersonic missiles with speeds and trajectories that are difficult to intercept, the growing capabilities of cyber warfare targeting command and control systems, and the rise of drone swarms as a means of overwhelming defenses through saturation. Additionally, advancements in sensor technologies and artificial intelligence have enabled the tracking of small, large, complex, and moving targets. These transformations do not necessarily imply that the aircraft carrier has become weak, but they do raise legitimate questions about the adequacy of the defensive philosophy established two decades ago.
At that time, conventional maritime threats were well-known and integrated into the carrier’s design, which relied on layered defenses and advanced damage control systems. However, between 2005 and 2025, the world experienced tremendous and rapid scientific and military advancements. China, for example, has surged in military spending and innovation, with its development rate increasing by approximately 250–300% between 2005 and 2025, making it one of the world’s closest competitors.
In contrast, the United States maintained its dominance, albeit at a slower pace, with an estimated development rate of 160–180%. Russia, on the other hand, achieved selective modernization while preserving its nuclear capabilities, with an estimated development rate of 140–160%.
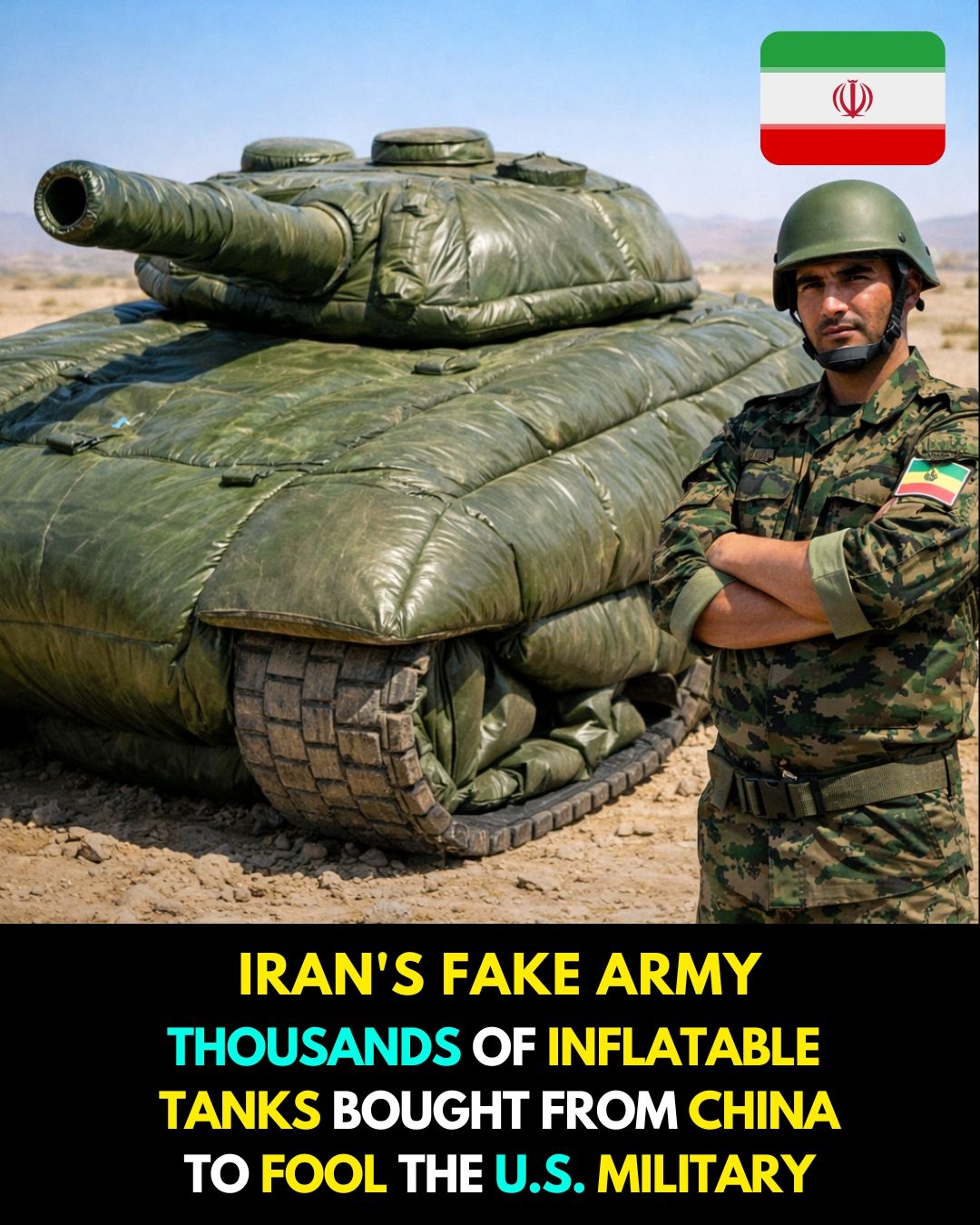
Iran, starting from a modest base, made a relatively significant leap in its missile and drone capabilities, with an estimated development rate of 300–350%. In this context, another question arises concerning the thinking of some countries that do not seek to emulate the United States in terms of fleet size or number of aircraft carriers, such as China, Russia, or Iran. Instead of engaging in a costly, conventional arms race, these countries’ military thinking (thinking outside the box) focuses on circumventing this model and seeking unconventional means to neutralize, disable, or directly destroy the platform.
Within this framework, discussions arise regarding technologies based on radiation, microwaves, or other directed energy sources. In principle, there is nothing to prevent the development of devices based on high-powered microwaves, electromagnetic pulses, or high-energy lasers. However, the potential role of these technologies, as currently understood, is not to melt or physically destroy the carrier’s hull, but rather to disable or confuse sensitive electronics, disable radar, navigation, and communication systems, or disrupt flight control systems on the carrier’s deck.
The idea of melting thick marine steel, armored hulls, or parts thereof with beams from combat range is unrealistic given current data, due to the enormous energy requirements, radiation dispersion, and the difficulty of precise targeting of a moving target protected by multiple layers of defense. However, we cannot confirm or deny that there are those who think and work in this field, shrouding their activities in absolute secrecy. Surprising the enemy with unexpected weapons has always been, and remains, a core element of military planning.
The real danger lies not in a super-radiation weapon, but in the integration of multiple fields, such as a cyberattack that disrupts combat command and control systems, electromagnetic jamming that confuses sensor systems, followed by a conventional physical attack. In such a scenario, the carrier transforms from a highly organized platform into a complex system suffering from information bottlenecks, one of the most serious challenges facing modern armies. Military history shows that what is described as secret science is not the discovery of new physical laws (which would be astonishing and groundbreaking if it occurred), but rather innovative applications of known sciences. The novelty lies in the application of these sciences.
This is often in the method of integration and deployment, not in the essence of the science itself. Therefore, despite the possibility of technologies whose details have not been disclosed, it is necessary to mention a Chinese and an Iranian development:
The media is currently reporting on a Chinese achievement dubbed the “aircraft carrier killer,” an air-launched ballistic missile likely designed to target American aircraft carriers and warships. Since this missile is hypersonic and employs a special guidance system, it is capable of maneuvering and evading anti-ship weapons.
Regarding Iran’s threats that a weapon capable of sinking a ship is more dangerous than the ship itself, Israeli sources are discussing the “Whale torpedo,” which is launched underwater, operates in a supercavitational cavity, and moves within a gas bubble that reduces its water resistance. At speeds of up to 360 km/h, it reduces the reaction time of targeted ships and makes interception difficult.
In conclusion, bypassing conventional weaponry has become a reality, and disabling an aircraft carrier is now, theoretically, possible. However, completely sinking one remains a secret weapon, not disclosed by those who possess it, in order to surprise the enemy.
This article is a translated piece of an Arabic version that appeared in Al Rai Al Youm.

 Pezeshkian: ‘Iran Will Not Surrender to Bullies’
Pezeshkian: ‘Iran Will Not Surrender to Bullies’ Israeli Soldiers Enforce Closure of Al Aqsa
Israeli Soldiers Enforce Closure of Al Aqsa 1 in 7 Displaced in Lebanon – NRC
1 in 7 Displaced in Lebanon – NRC Hormuz: End of an Era of Martime Dominance
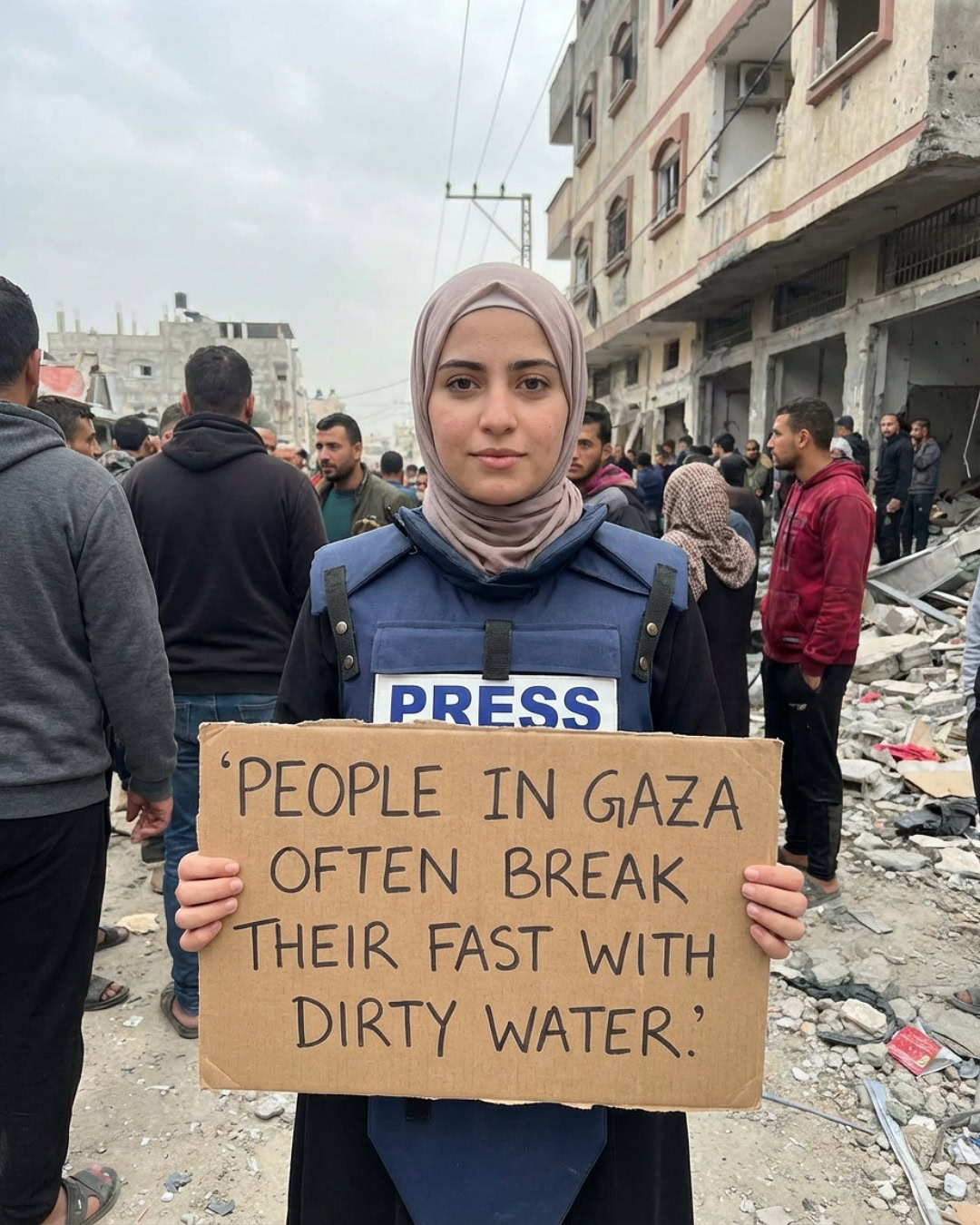
Hormuz: End of an Era of Martime Dominance Gaza Faces Massive Dust Storm
Gaza Faces Massive Dust Storm